The main objective for InfoSec in any organisation is to safeguard it’s data from a variety of threats. The CIA triad is a great foundational model to guide an organisations policies by ensuring data is confidential, accurate (integrity), and available to users that are authorized.
As the title suggests, InfoSec is made up of a wide range of disciplines. Some of the most common are:
- Network Security
- Application Security
- Operational Security
- Disaster Recovery and Business Continuity
- Cloud Security
- Physical Security
- Mobile Security
- Iot Security
Risks
In this world of InfoSec, risks refer to the potential for any malicious event to occur, that would cause damage to the assets of an organisation such as it’s data or infrastructure. This can be quantified based on the likelihood and how severe the impact is. The concept of risk includes vulnerabilities and threats. The management of risks requires appropriate identification and application of appropriate mitigating measures to minimize vulnerabilities.
Threats
In comparison, threats are the potential causes of incidents that could lead to harm to systems or organisations. Threats are not limited to hackers or criminals, but also could also be naturally occurring such as earthquakes, fires, floods, etc. The threats that organisations face exploit vulnerabilities in order to compromise the organisations security.
Vulnerabilities
Vulnerabilities are weaknesses in systems exploited by threats. They exist in many forms such as bugs in software, improper configurations, weak passwords, etc. Vulnerabilities being present does not always mean a system will be compromised. In order to reach a compromised state there needs to be a threat that is capable of exploiting the vulnerability.
Think of the original Nintendo Switch RCM jailbreak that utilised a vulnerability in the hardware of the switch that allowed unsigned code to run in order to jailbreak the console and allow third party apps to run.
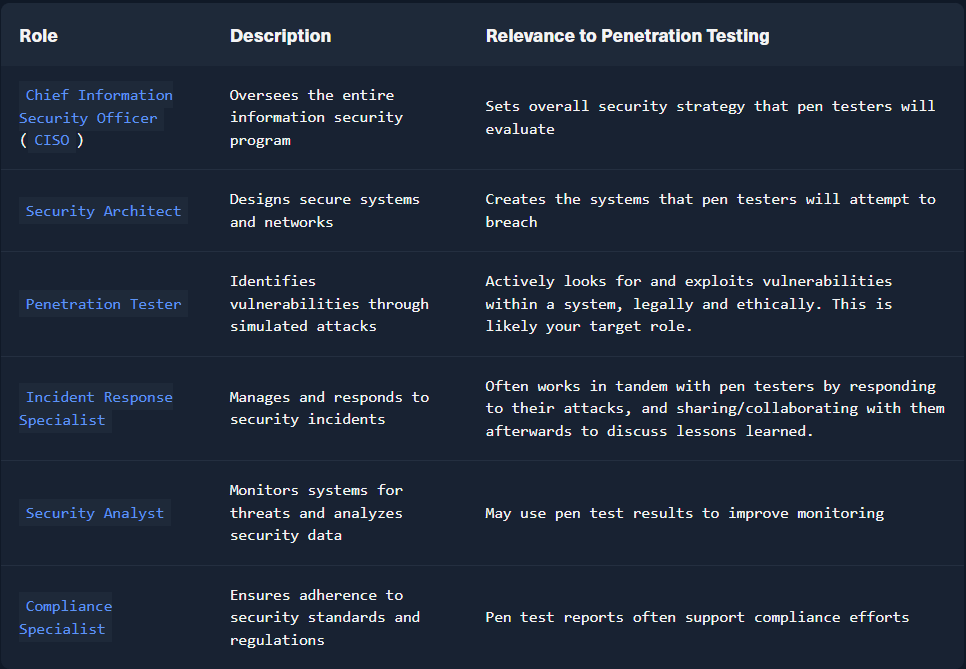
I have included a table from HackTheBox that outlines different roles, their description, and relevance to penetration testing below.

Leave a comment